“Zero Belief” is an often-misunderstood time period, it isn’t a product however a safety mannequin and related set of architectural rules and patterns. One of many principal challenges clients face is figuring out how Zero Belief rules could be utilized to IoT and the best way to get began with incorporating Zero Belief rules utilizing AWS IoT. On this weblog publish we talk about Zero Belief rules utilizing the NIST 800-207 Zero Belief tenets as a reference and AWS IoT companies which help Zero Belief by default and can be utilized to allow a Zero Belief IoT implementation.
What’s Zero Belief Safety?
Let’s begin with defining Zero Belief which is a conceptual mannequin and an related set of mechanisms that target offering safety controls round digital belongings. These safety controls don’t solely or essentially depend upon conventional community controls or community perimeters. It requires customers, units, and programs to show their identities and trustworthiness, and enforces fine-grained identity-based authorization guidelines earlier than permitting them to entry functions, knowledge, and different belongings.
Zero Belief rules are meant for a company’s total infrastructure which incorporates Operational Know-how (OT), IT programs, IoT and Industrial Web of Issues (IIoT). It’s about securing every part, all over the place. Conventional safety fashions rely closely on community segmentation, and provides excessive ranges of belief to units based mostly on their presence on the community. Compared, Zero Belief is a proactive and built-in method that explicitly verifies linked units no matter community location, asserts least privilege, and depends on intelligence, superior detection, and actual -time response to threats. With the proliferation of IoT units in enterprises and IIoT units in trade, rising cyber threats and hybrid work fashions, organizations are confronted with defending an expanded assault floor and new safety challenges. Zero Belief presents a greater safety mannequin due to the safety rules it makes use of and is an space of accelerating authorities and enterprise scrutiny.
A Zero Belief mannequin can considerably enhance a company’s safety posture by decreasing the only real reliance on perimeter-based safety. This doesn’t imply eliminating perimeter safety altogether. The place doable, use identification and community capabilities collectively to guard core belongings and apply Zero Belief rules working backwards from particular use instances with a concentrate on extracting enterprise worth and reaching measurable enterprise outcomes.
That will help you on this journey, AWS gives a variety of IoT companies which can be utilized with different AWS identification and networking companies to supply core Zero Belief constructing blocks as commonplace options that may be utilized to enterprise IoT and industrial IoT implementations.
Aligning AWS IoT with NIST 800-207 Zero Belief Rules
AWS IoT helps you undertake a NIST 800-207 based mostly Zero Belief structure (ZTA) by following the 7 Tenets of Zero Belief described right here:
1. All knowledge sources and computing companies are thought-about assets.
In AWS, we already be certain that all your knowledge sources and computing companies are modeled as assets. It’s intrinsic to our entry administration system. For instance, AWS IoT Core, AWS IoT Greengrass, and so forth. are thought-about assets in addition to companies like Amazon S3, Amazon DynamoDB, and so forth. which IoT units can securely name. Every linked machine should have a credential to work together with AWS IoT companies. All visitors to and from AWS IoT companies is shipped securely over Transport Layer Safety (TLS). AWS cloud safety mechanisms defend knowledge because it strikes between AWS IoT companies and different AWS companies.
2. All communication is secured no matter community location.
With AWS IoT companies, all communications are secured by default. Which means all communication between units and units and cloud companies are secured unbiased of community location by individually authenticating and authorizing each AWS API name over TLS. When a tool connects to different units or cloud companies, it should set up belief by authenticating utilizing principals equivalent to X.509 certificates, safety tokens, or different credentials. AWS IoT safety mannequin helps certificate-based authentication or customized authorizers for legacy units, authorization utilizing IoT insurance policies, and encryption utilizing TLS 1.2 and all communication between units and cloud companies are secured unbiased of community location. Together with sturdy identification offered by AWS IoT companies, Zero Belief requires least privilege entry management which controls the operations a tool is allowed to do after it connects to AWS IoT Core and to restrict the influence from authenticated identities that will have been compromised and this may be achieved utilizing AWS IoT insurance policies.
AWS gives machine software program to allow IoT and IIoT units to securely connect with different units and AWS companies within the cloud. AWS IoT Greengrass is an IoT open supply edge runtime and cloud service that helps construct, deploy, and handle machine software program. AWS IoT Greengrass authenticates and encrypts machine knowledge for each native and cloud communications, in order that knowledge isn’t exchanged between units and the cloud with out confirmed identification. One other instance is FreeRTOS. FreeRTOS is an open supply, real-time working system for microcontrollers that makes small, low-power edge units simple to program, deploy, safe, join, and handle. FreeRTOS consists of help for Transport Layer Safety (TLS v1.2) for safe communications and PKCS #11 to be used with cryptographic parts used for securely storing credentials. With AWS IoT Gadget Shopper you may securely join your IoT units to AWS IoT companies.
3. Entry to particular person enterprise assets is granted on a per-session foundation and belief is evaluated earlier than entry is granted utilizing least privileges wanted to finish the duty.
AWS IoT companies and AWS API calls grant entry to assets on a per-session foundation. IoT units must authenticate with AWS IoT Core and be licensed earlier than it could actually carry out an motion, so belief within the machine is evaluated by AWS IoT Core earlier than granting permissions. Each time a tool needs to connect with AWS IoT Core, it presents its machine certificates or customized authorizer to authenticate with AWS IoT Core, throughout which period IoT insurance policies are enforced to test if the machine is permitted to entry the assets it’s requesting. This authorization is just legitimate for the present session. The subsequent time the machine needs to attach it goes by the identical steps once more making this a per session entry sample. The identical applies if a tool needs to connect with different AWS companies through the use of AWS IoT Core credential supplier.
4. Entry to assets is decided by dynamic coverage —together with the observable state of consumer identification, software/service, and the requesting asset and should embody different behavioral and environmental attributes.
A core precept behind Zero Belief is that no IoT machine needs to be granted entry to different units and functions till assessed for threat and permitted throughout the set parameters of regular conduct. This precept applies completely to IoT units since they’ve restricted, steady and predictable behaviors by nature and its doable to make use of their conduct as a measure of machine well being. As soon as recognized, each IoT machine needs to be verified in opposition to baselined behaviors earlier than being granted entry to different units and functions within the community. There are a number of methods to detect machine state utilizing the AWS IoT Gadget Shadow characteristic and detect machine anomalies utilizing AWS IoT Gadget Defender. Entry insurance policies are utilized to a group of units, often known as a thing-group in AWS IoT and are evaluated at runtime earlier than entry is granted. Membership in a bunch is dynamic and could be configured to vary based mostly on machine conduct utilizing AWS IoT Gadget Defender. AWS IoT Gadget Defender makes use of Guidelines Detect or ML Detect options to find out the machine’s regular behaviors and any potential deviation from the baseline. As soon as an anomaly is detected, the machine could be moved to a quarantined group with restricted permissions based mostly on the static group’s coverage or could be disallowed from connecting to AWS IoT Core.
5. The enterprise displays and measures the integrity and safety posture of all owned and related belongings. No asset is inherently trusted. The enterprise evaluates the safety posture of the asset when evaluating a useful resource request. An enterprise implementing a ZTA ought to set up a steady diagnostics and mitigation (CDM) or related system to watch the state of units and functions and may apply patches/fixes as wanted.
AWS IoT Gadget Defender repeatedly audits and displays your fleet of IoT units and you should use different AWS companies for steady audit & monitoring of non-IoT parts and companies which can be utilized to judge the safety posture of an asset when evaluating a useful resource request. For instance, based mostly on the outcomes from auditing and monitoring your machine fleet utilizing AWS IoT Gadget Defender, you may take mitigation actions equivalent to putting a tool in a static factor group with restricted permissions, revoking permissions, quarantine the machine, apply patches to maintain units wholesome utilizing AWS IoT Jobs characteristic for over-the-air (OTA) updates, remotely connect with the machine for service or troubleshooting utilizing AWS IoT safe tunneling characteristic.
6. All useful resource authentication and authorization are dynamic and strictly enforced earlier than entry is allowed. It is a fixed cycle of acquiring entry, scanning and assessing threats, adapting, and frequently reevaluating belief in ongoing communication.
Zero Belief begins with “default deny” and no entry is granted with out correct authentication, authorization mixed with indicators from machine well being. AWS IoT companies carry out authentication and authorization earlier than entry is allowed and the identical is true with each AWS API name. Zero Belief requires the flexibility to detect and reply to threats throughout IoT, IIoT, IT and Cloud networks. Along with AWS IoT Gadget Defender, different AWS companies can be utilized for safety auditing, monitoring, alerting, machine studying and taking mitigation actions.
7. The enterprise collects as a lot data as doable in regards to the present state of belongings, community infrastructure and communications and makes use of it to enhance its safety posture.
You need to use IoT machine knowledge to make steady enhancements in safety posture with AWS IoT Gadget Defender. For instance, you can begin by turning on the AWS IoT Gadget Defender Audit characteristic of their AWS account to get a safety baseline for his or her IoT units. Utilizing the baseline, you may make steady enhancements to enhance their safety posture. You possibly can then add the AWS IoT Gadget Defender Guidelines Detect or ML Detect characteristic to detect anomalies continuously present in linked units and make enhancements based mostly on detect outcomes. As well as, with AWS IoT Gadget Defender customized metrics, you may outline and monitor metrics which might be distinctive to their machine fleet or use case. Along with machine knowledge, you will get insights from different knowledge collected on AWS (audit, logging, telemetry knowledge, analytics) and use AWS IoT options equivalent to AWS IoT Jobs to use patches to enhance safety posture and software program updates to enhance machine performance and AWS IoT Safe Tunneling to securely connect with units for troubleshooting and distant service if wanted and different AWS companies to make steady enhancements to an enterprise’s safety posture which may embody high-quality tuning permissions.
That will help you get began, you may strive the “Implementing Zero Belief with AWS IoT workshop” which may help you get palms on expertise leveraging a number of AWS IoT companies to securely and securely deploy industrial and industrial IoT units at scale utilizing the Zero Belief safety structure rules. Working by a state of affairs the place you’re accountable for deploying units exterior of your company perimeter, you’ll leverage AWS IoT Core, AWS IoT Gadget Defender, AWS IoT Gadget Administration and Amazon Easy Notification Service (SNS) to construct a resilient structure together with distinctive identification, least privilege, dynamic entry management, well being monitoring, and behavioral analytics to make sure the safety of your units and knowledge. After detecting a safety anomaly, it is possible for you to to research and take mitigation actions equivalent to quarantining an anomalous machine, securing connecting to the machine for distant troubleshooting, and apply a safety patch to repair machine vulnerabilities and preserve units wholesome.
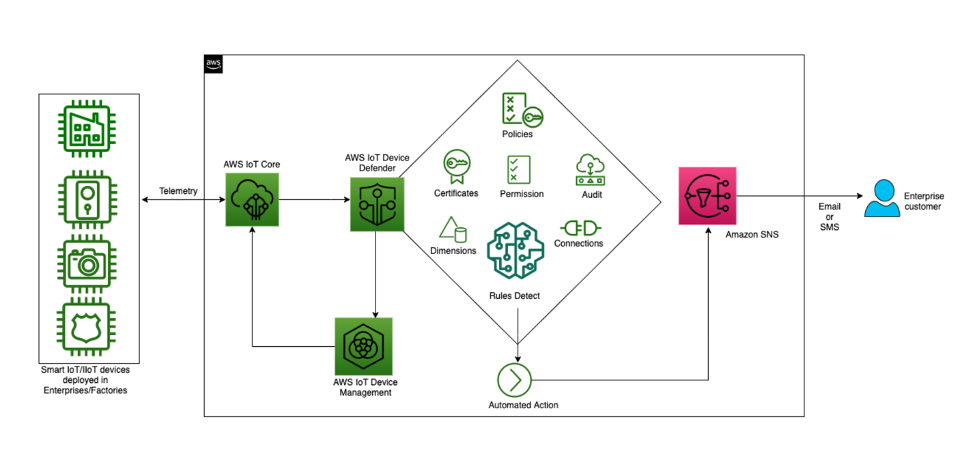
Implementing Zero Belief with AWS IoT workshop structure
Zero Belief Isn’t A Race; It’s A Steady Journey
Zero Belief requires a phased method and since each group is completely different, their journey will probably be distinctive based mostly on their maturity and the cyber safety threats they’re going through. Nevertheless, the core Zero Belief rules outlined on this weblog can nonetheless apply. For IoT and IIoT, AWS recommends a multi-layered safety method to safe IoT options finish to finish from machine to edge to cloud, together with the necessity to use sturdy identities, least privileged entry, repeatedly monitor machine well being and anomalies, securely connect with units to repair points and apply continuous updates to maintain units updated and wholesome. When transitioning to a Zero Belief structure, it’s not obligatory to tear and exchange current networks and eradicate conventional safety approaches to deploy Zero Belief. As an alternative, firms can transfer to Zero Belief over time utilizing an iterative method to guard one asset at a time till your complete atmosphere is protected, beginning with probably the most important belongings first. Earlier than decommissioning the standard safety controls with Zero Belief parts, guarantee you’ve performed complete testing. AWS recommends utilizing a Zero Belief method for contemporary IoT and IIoT units and mixing identification and community capabilities equivalent to micro community segmentation, AWS Direct Join and VPC Endpoints to attach legacy OT programs to AWS IoT companies. As well as, AWS presents AWS Outposts for sure workloads that are higher suited to on-premises administration and AWS Snowball Edge for functions needing to course of IIoT knowledge on the Edge. This permits the commercial edge to behave as a “guardian” to regionally interface with less-capable OT programs, bridging them to cloud companies with sturdy identification patterns. At all times work backwards from particular use instances and apply Zero Belief to your programs and knowledge in accordance with their worth. AWS presents a number of decisions with AWS safety companies and Companion options and gives clients with a better, sooner, and more cost effective path in the direction of enabling a Zero Belief implementation for IoT and IIoT workloads.
Study extra
Study extra about AWS’s worth pushed method to Zero Belief at Zero Belief on AWS
Concerning the authors

Ryan Dsouza is a International Options Architect for Industrial IoT (IIoT) at Amazon Internet Providers (AWS). Based mostly in New York Metropolis, Ryan helps clients architect, develop and function safe, scalable and extremely revolutionary options utilizing the breadth and depth of AWS platform capabilities to ship measurable enterprise outcomes. Ryan has over 25 years’ expertise in digital platforms, good manufacturing, vitality administration, constructing and industrial automation, and IIoT safety throughout a various vary of industries. Previous to AWS, Ryan labored in Accenture, SIEMENS, Normal Electrical, IBM and AECOM, serving clients with their digital transformation initiatives.

Syed Rehan as a Sr. Safety Product Supervisor at AWS performs a pivotal position in driving income development and launching strategic AWS safety companies. He collaborates carefully with cross-functional groups, leveraging his experience in cybersecurity, IoT, and cloud applied sciences to develop and launch revolutionary safety options that tackle clients’ evolving wants. Syed’s deep understanding of the market panorama and buyer ache factors allows him to determine profitable alternatives and spearhead the event of high-impact safety companies. By strategic product planning, roadmap creation, and efficient go-to-market methods, Syed contributes considerably to AWS’s income development and solidifies its place as a trusted chief in cloud safety.

